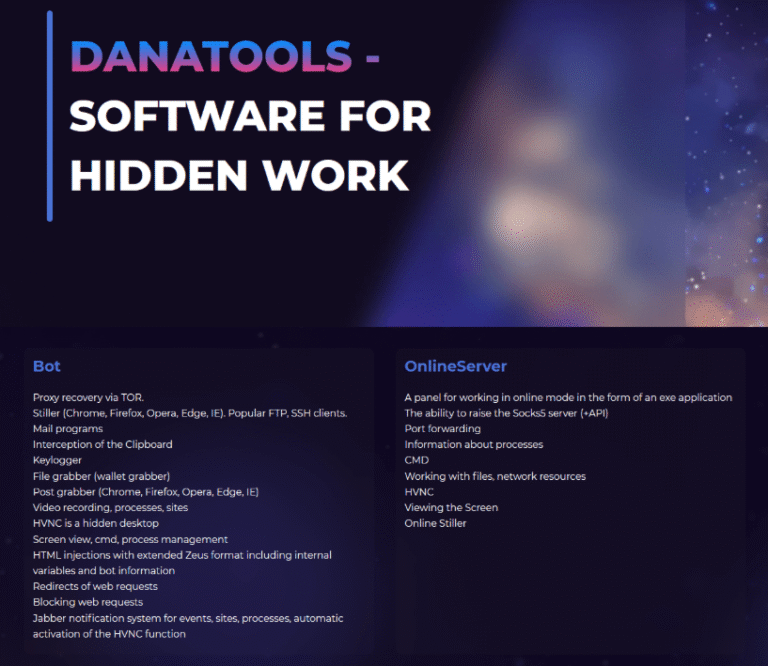
The U.S. government today unsealed criminal charges against 16 individuals accused of operating and selling DanaBot, a...
Cyber Security
May 25, 2025Ravie LakshmananThreat Intelligence / Software Security Cybersecurity researchers have disclosed a malware campaign that uses...
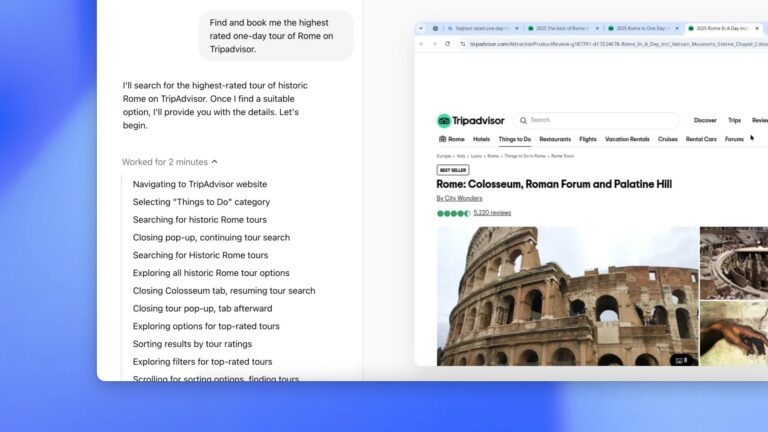
OpenAI says Operator Agent now uses the o3 model, which means it’s now significantly better at reasoning...
A Practical Blueprint for PDPA Compliance The Personal Data Protection Act (PDPA) is not just a legal...
Do you learn anything from sending thousands of phishing emails? YES, you do, and we want to...
In the rapidly evolving world of cybersecurity, businesses are increasingly seeking solutions that can protect them from...
Unlimited Access: Every Device on Your Network Can Talk to the Internet Back in 2018, I wrote...
As large language models (LLMs) become increasingly prevalent in businesses and applications, the need for robust security...
What is a HTTP security header? An HTTP security header is a response header that helps protect...
Whether you’ve invested in the iPhone 16 or have a legacy device, it’s important to consider using a virtual...