We have been using our data to identify researchers scanning the internet for a few years. Currently,...
Cyber Security
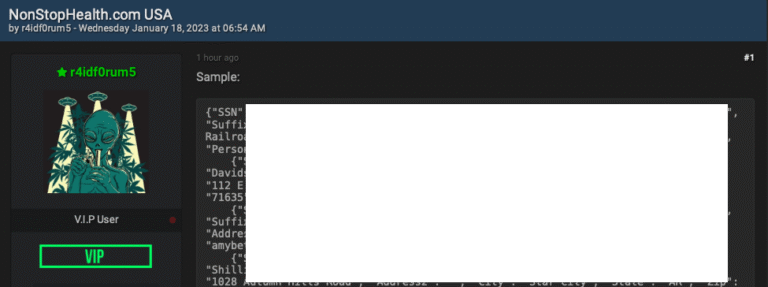
In what experts are calling a novel legal outcome, the 22-year-old former administrator of the cybercrime community...
May 19, 2025Ravie LakshmananMalware / Supply Chain Attack The official site for RVTools has been hacked to...
A new tool called ‘Defendnot’ can disable Microsoft Defender on Windows devices by registering a fake antivirus product,...
We are excited to announce a new partnership between Your Privacy Expert, a privacy consultancy firm led...
Our newest phishing training feature takes simulation insights to a whole new level. CyberPilot is one of...
In today’s digital world, small businesses are an increasingly likely target for cybercriminals. With cyberthreats like ransomware...
I Finally Segmented My Network… by Cutting the Ethernet Cable! For years, I’ve preached the value of...
Introduction Large Language Models (LLMs) have rapidly become integral to applications, but they come with some very...
How Injection Attacks Exploit Web Application Vulnerabilities Injection attacks occur when malicious input is inserted into a...