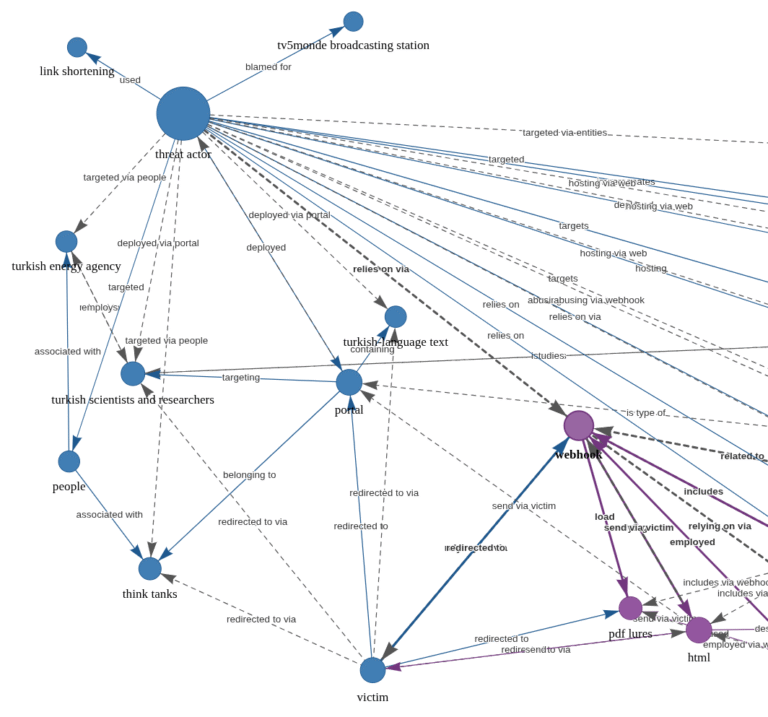
Threat intelligence observations show that a single threat actor is responsible for most of the active exploitation of...
Cyber Security
Security Information and Event Management (SIEM) platforms have become central to modern cybersecurity strategies. These systems collect,...
Ransomware: Because Who Doesn’t Want to Be Held Hostage by Their Own Files? You know that feeling...
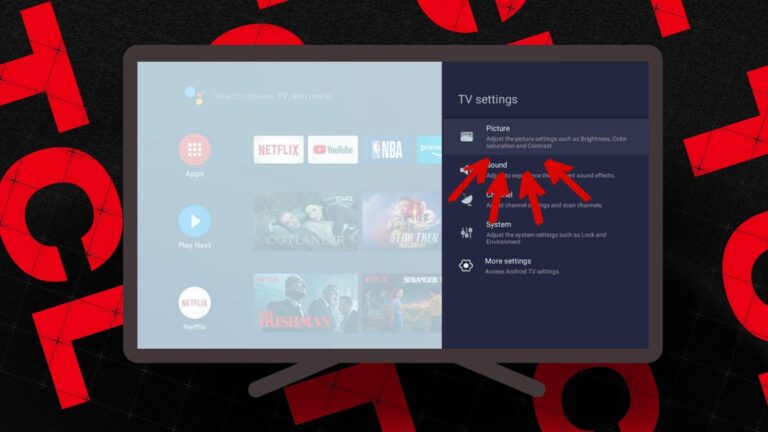
TCL / Elyse Betters Picaro / ZDNET Follow ZDNET: Add us as a preferred source on Google....
Unstructured text to interactive knowledge graph via LLM & SPO triplet extraction Courtesy of TLDR InfoSec Launches & Tools...
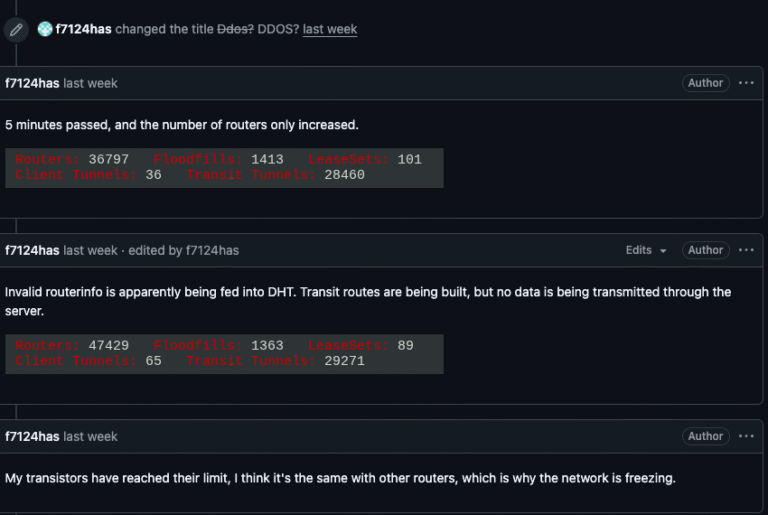
For the past week, the massive “Internet of Things” (IoT) botnet known as Kimwolf has been disrupting...
Ravie LakshmananFeb 12, 2026Vulnerability / Network Security A significant chunk of the exploitation attempts targeting a newly...
A member of the Crazy ransomware gang is abusing legitimate employee monitoring software and the SimpleHelp remote...
Cloud computing has transformed how businesses operate, but it’s also created new security challenges that traditional tools...
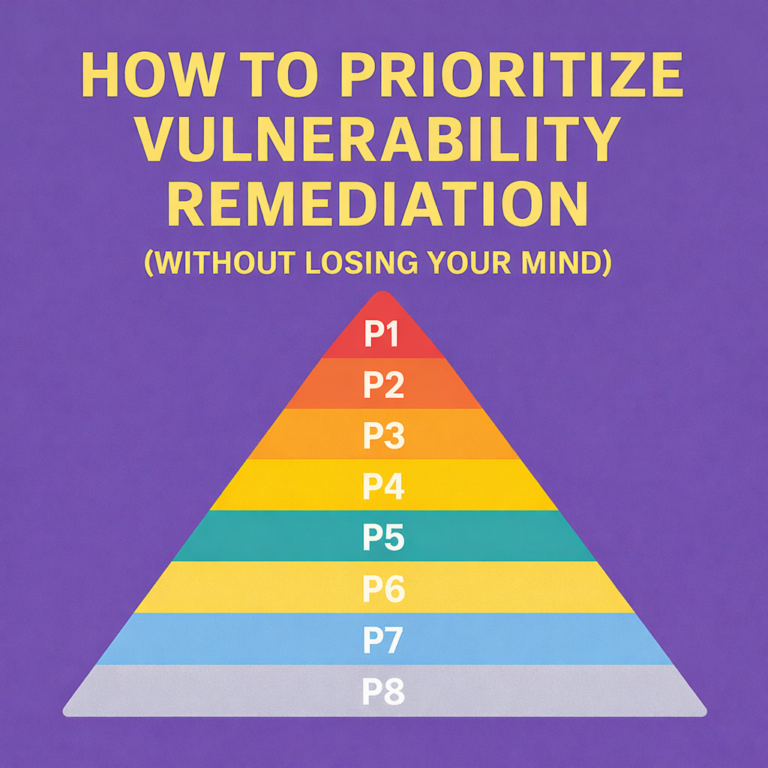
Let’s say you run a vulnerability scan and it finds 100 issues across your environment. Ten are...